It looks like my VPS root password has just been automatically (?) reset via the control panel, and I received a notification via email (I did not request a change).
I don't believe my Aeza billing account was compromised, considering I use two-factor authentication. Is this normal with Aeza?
Virtual machine password has been changed
The password of your virtual machine “....” has been changed successfully. Use the following credentials to manage your service:
Login: root
Password: ...
@Mumbly said:
It looks like my VPS root password has just been automatically (?) reset via the control panel, and I received a notification via email (I did not request a change).
I don't believe my Aeza billing account was compromised, considering I use two-factor authentication. Is this normal with Aeza?
I'm not sure if it's normal, but just chiming in to say that I also received this email.
@Mumbly said:
It looks like my VPS root password has just been automatically (?) reset via the control panel, and I received a notification via email (I did not request a change).
I don't believe my Aeza billing account was compromised, considering I use two-factor authentication. Is this normal with Aeza?
Virtual machine password has been changed
The password of your virtual machine “....” has been changed successfully. Use the following credentials to manage your service:
Login: root
Password: ...
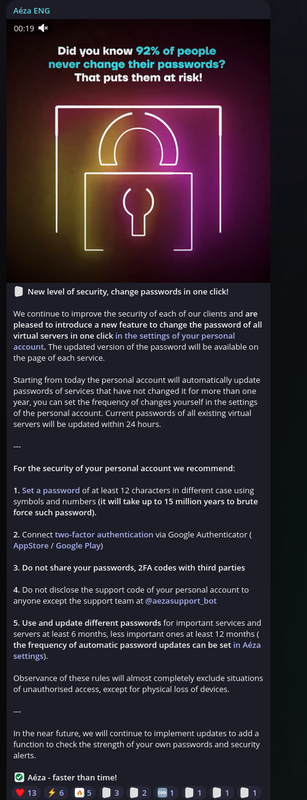
And this is from their Telegram, more flashy version:
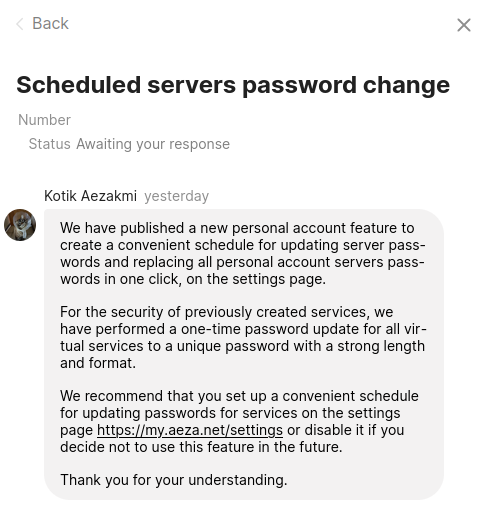
I guess they sent it to everyone but it somehow didn't email, its just a ticket in Support panel.
Good thing its not a hack or something, but it should've been communicated better(but I guess its a 1 eur vps).
I guess they sent it to everyone but it somehow didn't email, its just a ticket in Support panel.
Good thing its not a hack or something, but it should've been communicated better(but I guess its a 1 eur vps).
I guess they sent it to everyone but it somehow didn't email, its just a ticket in Support panel.
Good thing its not a hack or something, but it should've been communicated better(but I guess its a 1 eur vps).
At least it's well spent 1 euro
Even though this thing happened, I'm still happy with my 1 eur purchase. Its a steal, performance is amazing for the money.
@treesmokah said:
I guess they sent it to everyone but it somehow didn't email, its just a ticket in Support panel.
I did receive email up front about this change:
Stupid question from my side; I never thought about it this way, but providers (in this case Aeza) can always login as root to my VPS if they wanted to, right? Because apparently they can do an adhoc password reset and then use it to login via console.
@treesmokah said:
Even though this thing happened, I'm still happy with my 1 eur purchase. Its a steal, performance is amazing for the money.
Thanks again for sharing this deal. Best 1 euro I've spent in my life.
LinuxFreek.com — Thank you for your attention to this matter
@Freek said:
Stupid question from my side; I never thought about it this way, but providers (in this case Aeza) can always login as root to my VPS if they wanted to, right? Because apparently they can do an adhoc password reset and then use it to login via console.
Most providers can actually just get into your server quite easily, most of the time due to having qemu-guest-agent installed and running as root in your VM.
VMManager (what they use) somehow installs that shit even if you manually install an ISO IIRC.
So I guess if you want to be in the safest side (which is still not 100%, as you don't have the disk drive in your hand) then encrypting the drives is the best bet.
@zgato said: VMManager (what they use) somehow installs that shit even if you manually install an ISO IIRC.
VMManager is too intrusive (unlike VirtFusion) and to configure network for example they alter disk content before booting VM. On the other hand, VirtFusion uses external cloud-init disk and is able to cooperate with encrypted disks.
However I would like to note that LUKS (or any other disk encryption) makes unauthorized access to the virtual machine only harder but not impossible.
@Mumbly said:
It looks like my VPS root password has just been automatically (?) reset via the control panel, and I received a notification via email (I did not request a change).
I don't believe my Aeza billing account was compromised, considering I use two-factor authentication. Is this normal with Aeza?
Virtual machine password has been changed
The password of your virtual machine “....” has been changed successfully. Use the following credentials to manage your service:
Login: root
Password: ...
Hello, on April 30, passwords were reset on all services, this was done in order to increase the security of customer services.
There was also a post about it in our Telegram channel.
@alamdarzia said:
Statistics are not working, and is the ddos protection effective?
Hello, our attack protection works perfectly, our clients when attacked don't feel it on their servers.
Even with a 30gbps attack, your server will still work properly.
We care a lot about our customers and will not let evil people hack/break/disrupt your service.
Greetings to all users of this forum and our customers.
Saw a dispute about adding a bank or credit card to Stripe and here is what we want to tell you.
Adding a card to Stripe is absolutely safe, because Stripe will not steal your card or commit fraud with it, as it is a large superior payment aggregator.
I recommend you pay your bills via PayPal, we have it now and it is actively used by our customers.
@AezaHost when are you going to fix your shitty support? Used to be good (I even have a cool aeza emoji pack from your support guy) but now they're arrogant and just overall useless, it's always client's fault.
your antiddos is not great. I can almost boot off my VPS with a simple free stresser.
@zgato said: @AezaHost when are you going to fix your shitty support? Used to be good (I even have a cool aeza emoji pack from your support guy) but now they're arrogant and just overall useless, it's always client's fault.
your antiddos is not great. I can almost boot off my VPS with a simple free stresser.
Hello, let's communicate without insults and bad words.
Please clarify about our support, what exactly did you dislike or displease you?
If we talk about DDOS attacks, try to "put" your server down.
@zgato said: @AezaHost when are you going to fix your shitty support? Used to be good (I even have a cool aeza emoji pack from your support guy) but now they're arrogant and just overall useless, it's always client's fault.
your antiddos is not great. I can almost boot off my VPS with a simple free stresser.
Hello, let's communicate without insults and bad words.
Please clarify about our support, what exactly did you dislike or displease you?
If we talk about DDOS attacks, try to "put" your server down.
Can DM you screenshots before posting those here if you want, but if you're going to ignore them like in the OGF then I'll pass.
You should at least train your support. Answers like "i think" shouldn't be an answer to a client asking a question, they don't even bother to ask for a superior supp that can answer that.
@vercubynal said:
Is their website down right now?
It works just fine for me.
Back to VPS, I have bought it before I even started this thread, and experienced no downtime or cpu steal. Network and disk isn't bad too. Performance and quality is insane for this price.
Comments
Is it safe of using Russian company?
sure, same as US, CN they dont spy on their own companies
Mine never had any cpu steal or downtime since I got it(before I posted this thread). 1 eur for this is a steal.
As safe as any other company, proceed accordingly.
In my case it was using an anonymous account and crypto payments.
These are fair use cores, right?
I think so
It looks like my VPS root password has just been automatically (?) reset via the control panel, and I received a notification via email (I did not request a change).
I don't believe my Aeza billing account was compromised, considering I use two-factor authentication. Is this normal with Aeza?
I'm not sure if it's normal, but just chiming in to say that I also received this email.
Website: thomassen.sh
Got the same email just now
Amadex • Hosting Forums • root.hr
Same here. VPS works fine too.
I just found this is my Support center:
And this is from their Telegram, more flashy version:
I guess they sent it to everyone but it somehow didn't email, its just a ticket in Support panel.
Good thing its not a hack or something, but it should've been communicated better(but I guess its a 1 eur vps).
At least it's well spent 1 euro
Amadex • Hosting Forums • root.hr
Even though this thing happened, I'm still happy with my 1 eur purchase. Its a steal, performance is amazing for the money.
I did receive email up front about this change:
Stupid question from my side; I never thought about it this way, but providers (in this case Aeza) can always login as root to my VPS if they wanted to, right? Because apparently they can do an adhoc password reset and then use it to login via console.
Thanks again for sharing this deal. Best 1 euro I've spent in my life.
LinuxFreek.com — Thank you for your attention to this matter
Received the same email, thought mine was hacked.
https://microlxc.net/
Most providers can actually just get into your server quite easily, most of the time due to having qemu-guest-agent installed and running as root in your VM.
VMManager (what they use) somehow installs that shit even if you manually install an ISO IIRC.
So I guess if you want to be in the safest side (which is still not 100%, as you don't have the disk drive in your hand) then encrypting the drives is the best bet.
VMManager is too intrusive (unlike VirtFusion) and to configure network for example they alter disk content before booting VM. On the other hand, VirtFusion uses external cloud-init disk and is able to cooperate with encrypted disks.
However I would like to note that LUKS (or any other disk encryption) makes unauthorized access to the virtual machine only harder but not impossible.
Check our KVM VPS plans in 🇵🇱 Warsaw, Poland and 🇸🇪 Stockholm, Sweden
Back in stock, grab one before its too late
Billing system is buggered rip
Hello, on April 30, passwords were reset on all services, this was done in order to increase the security of customer services.
There was also a post about it in our Telegram channel.
Hello, it is as safe to use our website aeza.ru as aeza.net.
Aeza.ru is under the jurisdiction of the Russian Federation and aeza.net is under the jurisdiction of the United Kingdom.
Site aeza.ru differs only in the fact that some updates are not released there, but the services work in normal mode.
Hello, our attack protection works perfectly, our clients when attacked don't feel it on their servers.
Even with a 30gbps attack, your server will still work properly.
We care a lot about our customers and will not let evil people hack/break/disrupt your service.
Greetings to all users of this forum and our customers.
Saw a dispute about adding a bank or credit card to Stripe and here is what we want to tell you.
Adding a card to Stripe is absolutely safe, because Stripe will not steal your card or commit fraud with it, as it is a large superior payment aggregator.
I recommend you pay your bills via PayPal, we have it now and it is actively used by our customers.
@AezaHost when are you going to fix your shitty support? Used to be good (I even have a cool aeza emoji pack from your support guy) but now they're arrogant and just overall useless, it's always client's fault.
your antiddos is not great. I can almost boot off my VPS with a simple free stresser.
Hello, let's communicate without insults and bad words.
Please clarify about our support, what exactly did you dislike or displease you?
If we talk about DDOS attacks, try to "put" your server down.
Can DM you screenshots before posting those here if you want, but if you're going to ignore them like in the OGF then I'll pass.
You should at least train your support. Answers like "i think" shouldn't be an answer to a client asking a question, they don't even bother to ask for a superior supp that can answer that.
ayo just copped one
anyone know how their WAF works after pointing NS records?
the knowledge base is in russian(?) and free WAF tier doesn't get support. i can't find the panel it mentions
Where is it, i cant find it in payments options
Found it.
ServerStatus , slackvpn , linux mirrors
Recommended Providers: Servarica(aff) | HostBRR(aff) | SolidVPS(aff) | RackNerd(aff) | KuroIT(aff) | AlphaVPS(aff) | HostDare(aff)
Is their website down right now?
It works just fine for me.
Back to VPS, I have bought it before I even started this thread, and experienced no downtime or cpu steal. Network and disk isn't bad too. Performance and quality is insane for this price.
Aeza promo has IPv6?
Cloudcone | Crunchbits | Dartnode | Dedirock | Georgedatacenter | Gigahost | Hostbilby | Host-c | Hostdzire | Hostsailor | Namecrane | Nuyek | Realtoxmedia | Servarica | Terabit | Tnahosting | Virmach